By continuing to browse the site, you agree to our use of cookies. Check its details of the Privacy Policy and Cookies.
Accept 
The essence of the service is the on-going attention paid to the reliability of the cloud environment, the application it maintains and all the systems installed in it.
As part of our 24/7 monitoring and support service, our team:
● respond to all attempts to breach security,
● ensure that the application can use the necessary resources to function smoothly and efficiently,
● check the availability, compatibility, consistency and uninterrupted operation of specific services,
● monitor the backups for the correctness and all resources for consistency,
● verify system components validity,
● ensures updates, including safety updates.
The service is implemented on two levels: automatic and with a team of engineers. Its primary purpose is to ensure seamless continuity in the functioning of the cloud environment, the systems installed in it, and the applications it maintains.
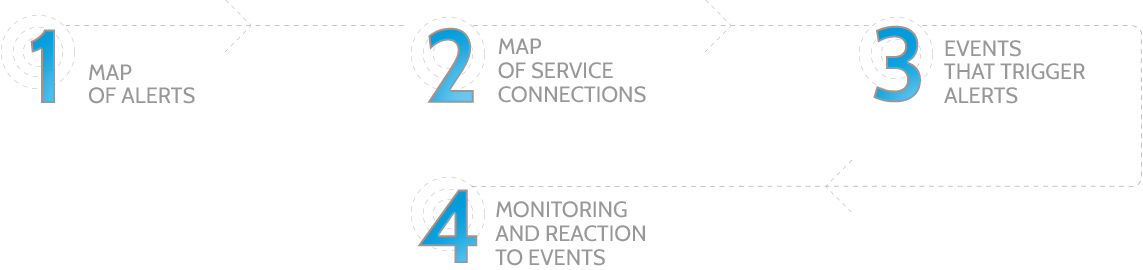
The properly configured automated monitoring system detects all incidents, especially alarming ones and emits alerts, giving them the following categories:
● notification,
● warning,
● or failure.
Our team of engineers respond to the abovementioned alerts for in accordance with the accepted procedures by:
● diagnosing the problem,
● indicating solutions and immediately implementing them,
● or notifying the client, if a given alert concerns an application or a system whose maintenance is the responsibility of the client.
With the complete security of all resources in mind, System Administrators begin their work with the configuration of key security rules that, over time, are adjusted and adapted to the current needs, based on the observation of potential threats. The knowledge gained from this is used in the process of improving protective mechanisms.
The monitoring and support service is used both by clients who do not have their own System Administrators who could manage and maintain the environment as well as by companies with an extensive organisational structure, where effective, multi-level distribution of information on emerging incidents and threats is critical.
The service includes the development or improvement of a “call tree”, which significantly facilitates communication and separation of tasks in the event of various types of failures and threats. The structure of the tree covers developers teams, security professionals, administrators and external companies, if necessary.
Provide the necessary information and send your form and we will contact you immediately to learn the details and provide a cost estimate for you.
Proper preparation significantly influences the subsequent course and success of the action, so before we begin the implementation, we ask all our clients interested in the monitoring and support service to:
- make an inventory of application and infrastructure resources,
- determine the application and business dependencies among the different environment and application elements,
- help with the development of the ”call tree” and notification scenarios preparation.
Working in a distributed team, we use modern communication and project management tools, such as Slack, Redmine and Jira.
To implement the monitoring and support service, we use the dedicated Amazon Cloud solution – AWS CloudWatch – which allows us to collect data and track specific indicators, set alerts and automatically respond to changes in AWS Cloud resources. We also use the AWS CloudFormation, a service that allows developers and system administrators to easily create and manage connected AWS Cloud resource collections as well as provision and update them in an orderly and predictable manner.
Most notably, what will enable you to focus on further business development, i.e. the full security of all resources. Knowing that you have complete control over the environment and that an experienced team of engineers has the best tools and skills to detect and eliminate threats early enough, you are able to make well thought out business decisions that are not based on fear.
In addition, the monitoring of the used resources allows you to precisely identify future technological needs and budget for them appropriately.
Provide the necessary information and send your form and we will contact you immediately to learn the details and provide a cost estimate for you.