Security investigator - Amazon Detective
Cybersecurity is one of the priorities in the age of the information society, where data is a value in itself. It is worth paying attention to properly designed security solutions. To be able to ensure compliance with the required standards and the highest quality of solutions, Amazon Web Services has prepared a number of services in the Security category: Amazon GuardDuty, Amazon Macie or AWS SecurityHub (download the infographic), which help provide the highest protection. In addition, the existing level of security at the customer can be extended with dedicated solutions of AWS partners. All these services and solutions enable the detection and elimination of security errors. However, when the cause lies deeper, Amazon Detective comes to the rescue.
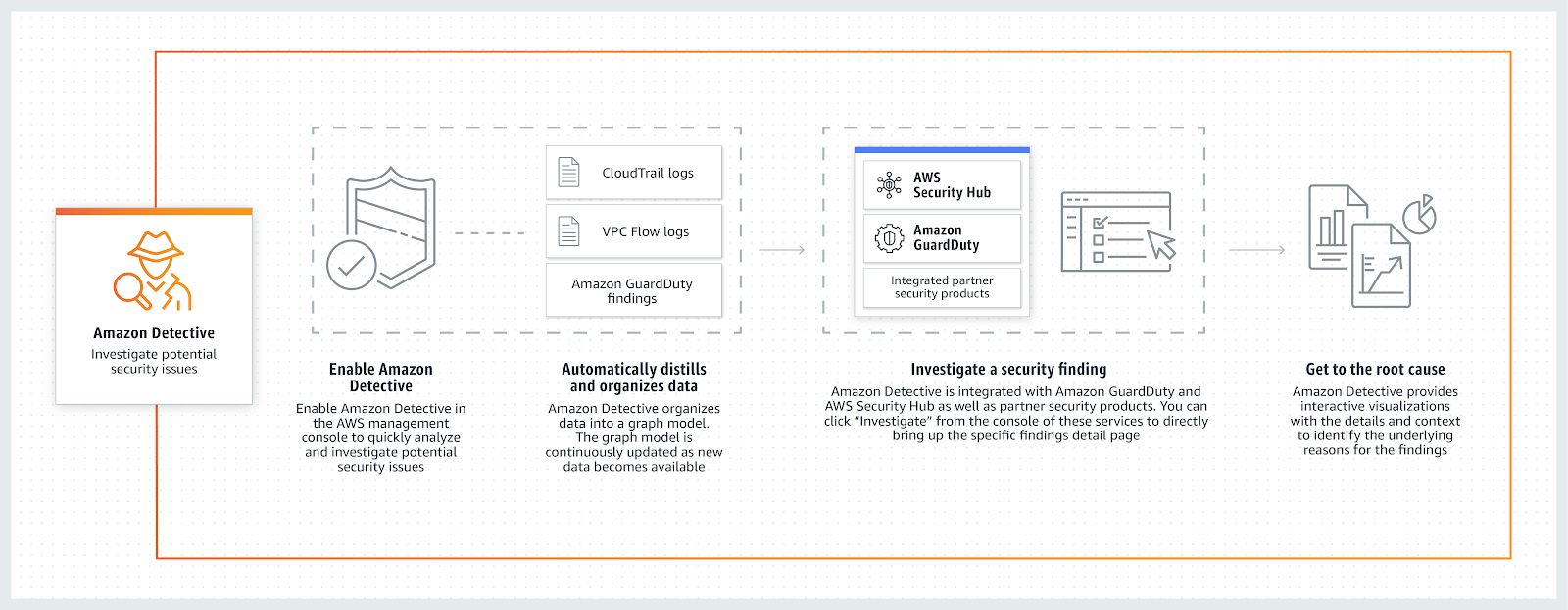
 Amazon Detective is the latest security service from the AWS family. It uses machine learning, statistical analysis and graph theory, in combination with AWS resource log data to detect potentially dangerous activities and security issues. It allows clients to view summaries and analytical data related to events in AWS CloudTrail as well as VPC Flow Logs. For customers who have Amazon GuardDuty enabled, Amazon Detective also processes the results obtained from GuardDuty.
Amazon Detective is the latest security service from the AWS family. It uses machine learning, statistical analysis and graph theory, in combination with AWS resource log data to detect potentially dangerous activities and security issues. It allows clients to view summaries and analytical data related to events in AWS CloudTrail as well as VPC Flow Logs. For customers who have Amazon GuardDuty enabled, Amazon Detective also processes the results obtained from GuardDuty.
So how does the service work? Amazon Detective allows you to automate heavy operations related to the processing of large amounts of data from AWS logs, in order to determine the cause of the threat and its impact on security. It uses machine learning models to create graphical presentations of account behaviour and helps answer questions such as “is this a custom API call for this role?” or “is this increase in traffic expected for this instance?” There is no need to write new code, configure or customize your own queries.
Source: https://aws.amazon.com/detective/
The Amazon Detective service can be used in 3 cases:
- Triage security findings – a trio is usually the first step in an investigation process, necessary to decide if an incident is an actual or apparent threat. Thanks to the visualization provided by the Amazon Detective service, it is possible to determine the incident related IP addresses, resources and accounts of AWS as well as activities at the time when the event took place and determine whether it is really malicious activity or a false alarm.
- Incident investigation – Amazon Detective allows conducting an investigation process, with in-depth analysis of malicious activity detected by services such as Amazon GuardDuty, along with determining its impact on security. The analysis consists of comparing archival activities with current ones and identifying unusual patterns to determine why the current action caused an alert.
- Threat hunting – this is a proactive analysis, which aims to locate hidden threats based on hypotheses and tips. The service provides explanations based on time analysis and the possibility of sinking to determine changes that have occurred in a given time period.