Amazon GuardDuty - protection with one click
Amazon GuardDuty is a service that aims to constantly monitor and manage cloud threats. It provides protection for AWS accounts and workloads. It owes its effectiveness to quick risk analysis and simple operation – just a few clicks to fully configure it. In addition, it does not require the implementation and maintenance of specialized software or infrastructure, which, as a result, does not burden existing applications..
Amazon GuardDuty found its application, among others in the financial or telecommunications industries. The service is based on access to embedded detection techniques, optimized and developed specifically for the needs of the cloud. In addition, the automated process allows you to design economic architecture while ensuring security without additional costs for the customer. GuardDuty – is an Intrusion Detection tool, that is, it detects unusual behaviors that may potentially indicate that the site is being attacked, hacked or malicious software got on the server.
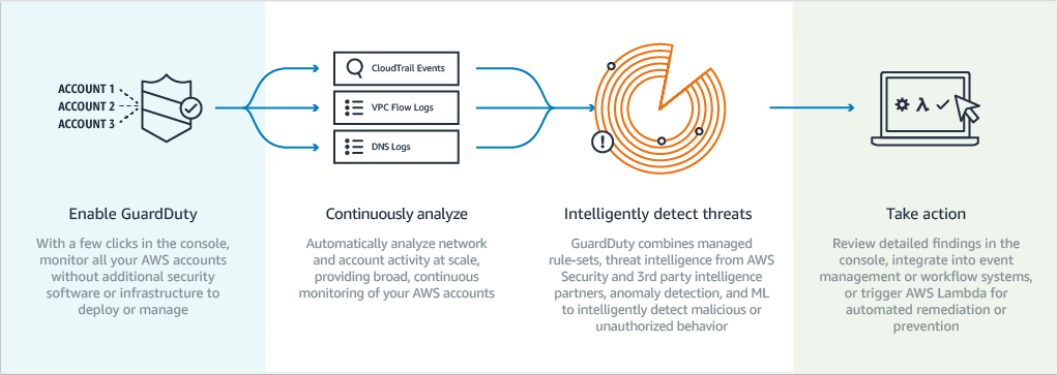
How does GuardDuty work?
 Source: Amazon Web Services
Source: Amazon Web Services
The above graphic illustrates the scheme of operation of the entire service.
It owes its effectiveness to intelligent detection of threats, based on data from AWS CloudTrail or logs from DNS and from the AWS VPC Flow Logs service (tracking network communication in VPC). In detecting abnormal activities related to the network or account, it uses machine learning, eg GuardDuty sends a notification if the API is invoked by a malicious IP address.
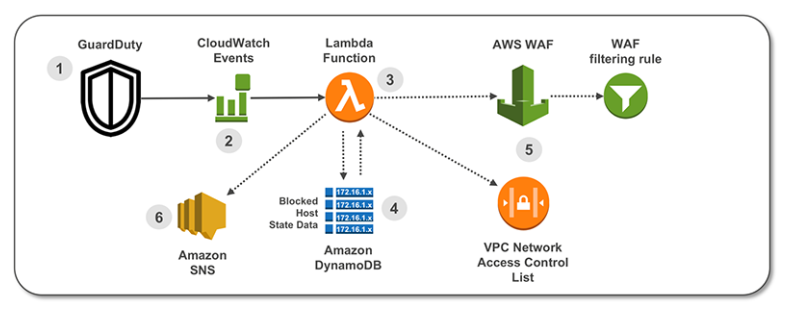
With AWS CloudWatch, event data can be redirected to other target actions. The AWS Web Application Firewall (WAF) and VAC NACL are routed and updated with AWS Lambda’s help. AWS WAF is a web application firewall that helps protect Internet applications from typical network exploits that can affect application availability, compromise security, or consume excessive resources.
Detected threats in Amazon GuardDuty are categorized on three risk levels: low, medium and high, which are determined by means of numerical values. The values oscillate from 0 to 10 on a ten-point scale and allow for the hierarchization of emerging threats. However, the point scale is not fully used – AWS leaves a range between 9.0 and 10.0 for future use.
The threat levels are as follows:
- low 0.1 – 3.9 – indicates suspicious activity that was blocked before it violated resources,
- medium 4.0 – 6.9 – indicates suspicious activities that require immediate verification;
- high 7.0 – 8.9 – indicates that resources are at risk and actively used for unauthorized purposes.
Let’s take a closer look at the GuardDuty component
Below is a template diagram that is created by AWS CloudTrail. It is a service that ensures security compliance, allows you to freely manage the AWS account resources and conduct an operational audit and risk audit. Thanks to it, monitoring account activity and managing activities in the AWS infrastructure, allow you to track changes in resources, analyze security and solve emerging problems.
 Source: Amazon Web Services
Source: Amazon Web Services
Access management in GuardDuty
Launching the Amazon GuardDuty service requires just a few clicks on the AWS console. After enabling it, the analysis of continuous streams of account and network activity begins immediately. It is worth remembering that the analysis data is stored for 90 days. It is also possible to automate the process of transferring this data to the S3 service, where it can be collected without any time limit.
The first step in starting the service is giving rights to individual IAM identities (roles, users or groups).
The policy policy template that should be added to IAM can be found in the Amazon GuardDuty User Guide.
The next step is to configure the role related to the service in order to delegate GuardDuty permissions. The role associated with the AWS service (in this case GuardDuty) is a unique type of IAM role. This role has the rights defined to make calls on behalf of the user. Modifying the role settings is not possible, and the only option is to delete the role via the IAM console.
After performing these two operations, GuardDuty starts scanning for threats. Detailed deployment of both templates can be found here.
An example of using GuardDuty in a client’s project
The client with whom we implemented the solution is a global leader providing secure logon (VPN) systems to the Internet, eg in cafes, schools, universities and BYOD solutions for corporate clients.
Prior to implementation, the client expected estimation of the cost of the solution.
Based on the number of requests coming to CloudTrail and the size of VPCFlowLogs logs (for an account of about 40 instances with moderate network utilization), we calculated the cost at about 12 – 14 USD per month. Implementation is quite simple, because the activation comes down to a single click.
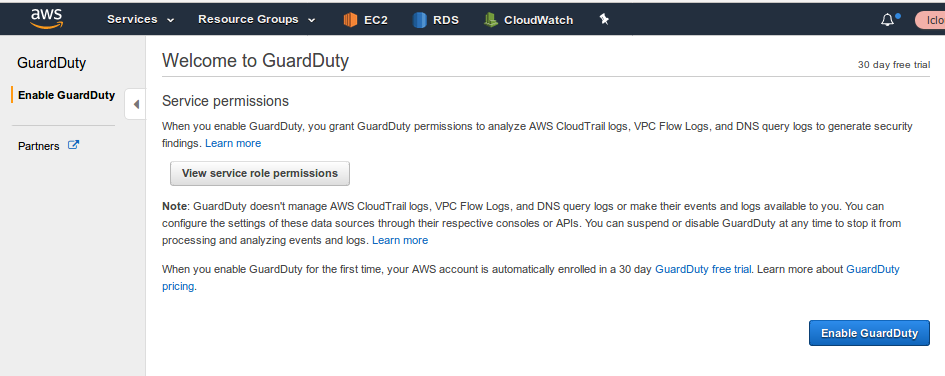 AWS console – GuardDuty service – input screen
AWS console – GuardDuty service – input screen
AWS alone, “live” analyzes events, and when they match the pattern, it marks them as “findings”.
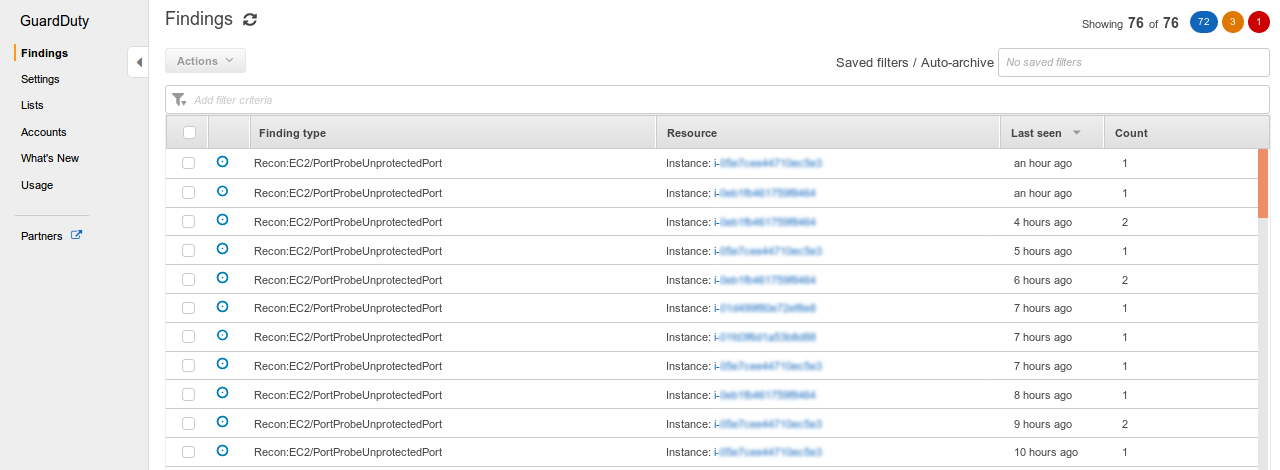 AWS console – GuardDuty service – event analysis
AWS console – GuardDuty service – event analysis
Events are categorized into groups, depending on the importance and then an event is generated, which is sent to CloudWatch, where it can filter them appropriately. In response to an AWS event, notification may be sent.
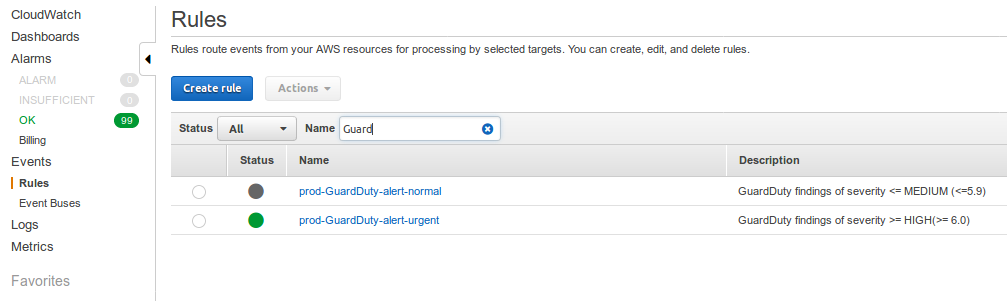 AWS console – GuardDuty service – notification
AWS console – GuardDuty service – notification
In each event reported by GuardDuty, there is a description of the risk and events (date, time, type of event, interface, server details) and a link to the AWS documentation, with a detailed description of the risk.
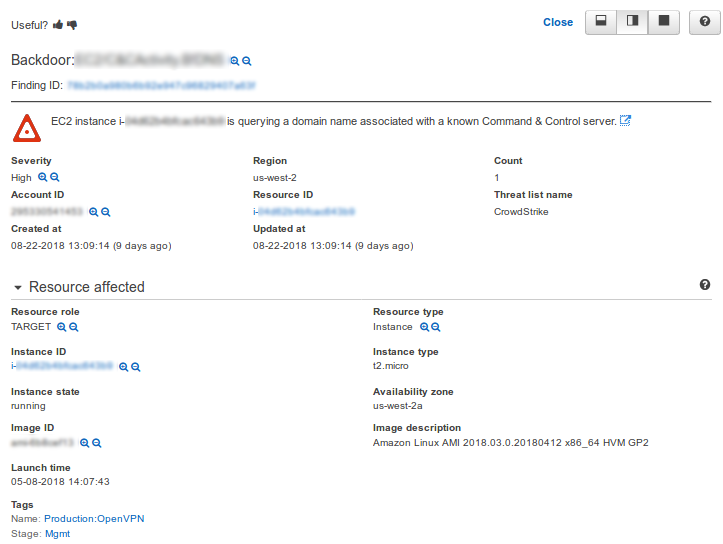
AWS console – GuardDuty service – description of the event and risk
What is the price of security?
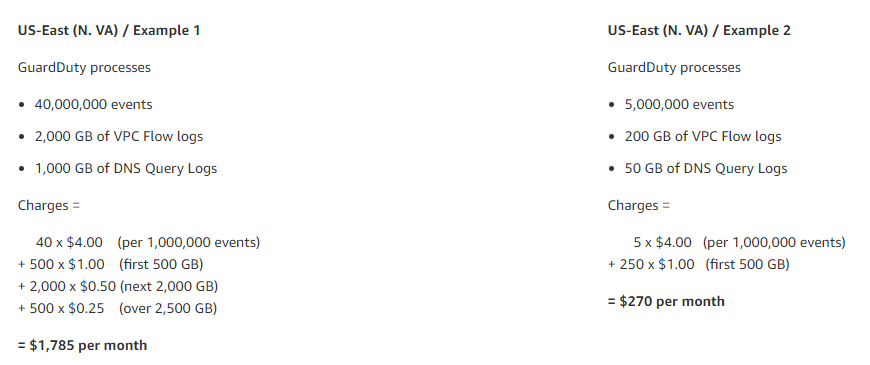
The service is priced by AWS in two dimensions:
- based on the number of registered events by AWS CloudTrail
and
- based on data collected from Amazon VPC Flow Log and DNS Log listeners
Prices also vary due to the availability of the service in your region. The table of fees can be found here. Below are examples of the monthly costs for Northern Virginia in the east of the USA.
 Source: Amazon Web Services
Source: Amazon Web Services
Benefits from the implementation of Amazon GuardDuty
The benefits of launching the Amazon GuardDuty include accurate detection of risks at the account level, where the service provides a quick detection and determination of access violations that may be negative if not monitored in real time.
Continuous monitoring without additional costs is a huge plus, thanks to the lack of the need to implement and maintain specialized software.
You only pay for the ability to detect threats when you use the service. Amazon Web Services, thanks to constant innovations and work on the development of individual services, provides top-class solutions that are specially developed and optimized for the cloud environment.
GuardDuty, thanks to three levels of security for results (high, medium and low) also allows you to adjust the security priorities.
Implementation with one click makes the service almost a “plug and play” solution, and the whole process is fully automated, allowing you to run GuardDuty on several accounts at the same time.
